Benutzer:Weblaie/Übersetzungswerkstatt
Linux-Malware umfasst Viren, Trojaner, Würmer und andere Schadsoftware, die das Linux-Betriebssystem beeinträchtigen. Linux, Unix und andere Unix-ähnliche Betriebssysteme werden im Allgemeinen als sehr gut geschützt, aber nicht immun, vor Schadsoftware angesehen. [1][2]
Es gibt bislang keine weit verbreitete Linux-Malware-Bedrohung in der Art, wie sie dem Microsoft Windows-Betriebssystem gegenübersteht. Dies wird häufig der geringen Zahl der Benutzer, die Linux als Desktop-Betriebssystem nutzen[1], dem fehlenden |Root-Zugang und schnellen Updates zu die meisten Linux-Sicherheitslücken zugeschrieben[2].
Die Anzahl an Schadprogrammen, die einschließlich Viren, Trojanern und anderen Bedrohungen speziell für Linux geschrieben ist, ist in den letzten Jahren deutlich angewachsen und hat sich im Jahr 2005 von 422 auf 863 verdoppelt.[3]
Linux vulnerability
Like Unix systems, Linux implements a multi-user environment where users are granted specific privileges and there is some form of access control implemented. To gain control over a Linux system or cause any serious consequence to the system itself, the malware would have to gain root access to the system.[2]
Shane Coursen, a senior technical consultant with Kaspersky Lab, claims, "The growth in Linux malware is simply due to its increasing popularity, particularly as a desktop operating system ... The use of an operating system is directly correlated to the interest by the malware writers to develop malware for that OS."[3] Rick Moen, an experienced Linux system administrator, counters that:
Some Linux users run Linux-based anti-virus software to scan insecure documents and email which comes from or is going to Windows users. SecurityFocus's Scott Granneman stated:
Because they are predominantly used on mail servers which may send mail to computers running other operating systems, Linux virus scanners generally use definitions for, and scan for, all known viruses for all computer platforms. For example the open source ClamAV "Detects ... viruses, worms and trojans, including Microsoft Office macro viruses, mobile malware, and other threats."[4]
Viruses and trojan horses
The viruses listed below pose a potential, although minimal, threat to Linux systems. If an infected binary containing one of the viruses were run, the system would be infected. The infection level would depend on which user with what privileges ran the binary. A binary run under the root account would be able to infect the entire system. Privilege escalation vulnerabilities may permit malware running under a limited account to infect the entire system.
It is worth noting that this is true for any malicious program that is run without special steps taken to limit its privileges. It is trivial to add a code snippet to any program that a user may download and let this additional code download a modified login server, an open mail relay or similar and make this additional component run any time the user logs in. No special malware writing skills are needed for this. Special skill may be needed for tricking the user to run the (trojan) program in the first place.
The use of software repositories significantly reduces any threat of installation of malware, as the software repositories are checked by maintainers, who try to ensure that their repository is malware-free. Subsequently, to ensure safe distribution of the software, checksums are made available. These make it possible to reveal modified versions that may have been introduced by e.g. hijacking of communications using a man-in-the-middle attack or via a redirection attack such as ARP or DNS poisoning. Careful use of these digital signatures provides an additional line of defense, which limits the scope of attacks to include only the original authors, package and release maintainers and possibly others with suitable administrative access, depending on how the keys and checksums are handled.
Worms and targeted attacks
The classical threat to Unix-like systems is vulnerabilities in network daemons, such as SSH and web servers. These can be used by worms or for attacks against specific targets. As servers are patched quite quickly when a vulnerability is found, there have been only a few widespread worms of this kind. As specific targets can be attacked through a vulnerability that is not publicly known there is no guarantee that a certain installation is secure. Also servers without such vulnerabilities can be successfully attacked through weak passwords.
Web scripts
Linux servers may also be used by malware without any attack against the system itself, where e.g. web content and scripts are insufficiently restricted or checked and used by malware to attack visitors. Typically a CGI script (meant for leaving comments) by mistake allows inclusion of code exploiting vulnerabilities in the web browser.
Buffer overruns
Older Linux distributions were relatively sensitive to buffer overrun attacks: if the program did not care about the size of the buffer itself, the kernel provided only limited protection, allowing an attacker to execute arbitrary code under the rights of the vulnerable application under attack. Programs that gain root access even when launched by a non-root user (via the setuid bit) were particularly attractive to attack. However as of 2009 most of the kernels include address space layout randomization (ASLR), enhanced memory protection and other extensions making such attacks much more difficult to arrange.
Cross-platform viruses
A new area of concern identified in 2007 is that of cross-platform viruses, driven by the popularity of cross-platform applications. This was brought to the forefront of malware awareness by the distribution of an OpenOffice.org virus called Badbunny.
Stuart Smith of Symantec wrote the following:
"What makes this virus worth mentioning is that it illustrates how easily scripting platforms, extensibility, plug-ins, ActiveX, etc, can be abused. All too often, this is forgotten in the pursuit to match features with another vendor... [T]he ability for malware to survive in a cross-platform, cross-application environment has particular relevance as more and more malware is pushed out via Web sites. How long until someone uses something like this to drop a JavaScript infector on a Web server, regardless of platform?"[5]
Social engineering
As is the case with any operating system, Linux is vulnerable to malware that tricks the user into installing it through social engineering. In December 2009 a malicious waterfall screensaver was discovered that contained a script that used the infected Linux PC in denial-of-service attacks.[6]
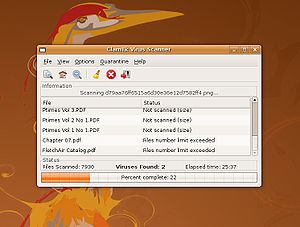
Anti-virus applications
There are a number of anti-virus applications available for Linux, most of which are designed for servers, including:
2
Threats
The following is a partial list of known Linux malware. However, few if any are in the wild (with the exception of Android malware), and most have been rendered obsolete by Linux updates. Known malware is not the only or even the most important threat: new malware or attacks directed to specific sites can use vulnerabilities previously unknown to the community or unused by malware.
Trojans
2
Viruses
2
Worms
2
See also
- List of computer viruses
- List of computer viruses (Numeric)
- List of computer viruses (A-D)
- List of computer viruses (E-K)
- List of computer viruses (L-R)
- List of computer viruses (S-Z)
References
External links
Vorlage:Linux Vorlage:Malware {{DEFAULTSORT:Linux Malware}} [[Category:Linux malware| ]] [[Category:Linux]]
- ↑ a b Scott Granneman: Linux vs. Windows Viruses. October 2003. Abgerufen am 6. März 2008.
- ↑ a b c Ray Yeargin: The short life and hard times of a linux virus. July 2005. Abgerufen am 24. Juni 2008.
- ↑ a b Andy Patrizio: Linux Malware On The Rise. April 2006. Abgerufen am 8. März 2008.
- ↑ ClamAV: Clam AntiVirus 0.96 User Manual. 2010. Abgerufen am 22. Februar 2011.
- ↑ Stuart Smith: Bad Bunny. June 2007. Abgerufen am 20. Februar 2008.
- ↑ Kristian Kissling: Malicious Screensaver: Malware on Gnome-Look.org. December 2009. Abgerufen am 12. Dezember 2009.